Half of all Chrome users install at least one additional extension. For corporate users, that number reportedly goes up to 99%.
Browser extensions are great. They help hide ads, fill out forms and passwords, block cookie banners, fix spelling, and manage tabs. But in order to do that, they need permissions. Sometimes those are limited to a particular website, but in many cases, they come in the dreaded form of “It can: Read and change all your data on all websites”. That should give you pause.
Not Chrome specific
This guide focuses on Chrome as it’s the most popular browser, but most sections apply to other browsers as well.
What’s the worst that could happen?
That sounds scary, but how would a malicious or compromised extension actually exploit that?
- UI spoofing: It could alter displayed bank balances and transfers or silently replace recipient details when making a transfer.
- That’s why some banks ask you to confirm a summary of what you are about to do in an extra app. In practice, almost no one double-checks this.
- Data exfiltration: Depending on permissions, it can access your browsing history, clipboard contents, cookies, and session tokens (allowing an attacker to log in as you).
- Credential theft: It can spy on what you type, modify forms, and in some cases intercept autofill credentials, even from password managers (although there are some protections against this).
- Malware delivery: It can redirect to malicious sites or download malware.
- Account takeover: When logged into Google Workspace, it can send emails or access Drive contents.
- Network hijacking: With the proxy permission, it can route traffic through attacker-controlled servers.
- Polymorphic extensions: These pose as legitimate extensions but then mimic the icon and UI of other extensions to steal data.
How can it happen?
Let’s go through all the ways an extension might get compromised.
Security vulnerability
No software is 100% safe against vulnerabilities. 100+ vulnerabilities are reported in software every day.
Browser extensions are particularly at risk since they are often developed by hobbyists and abandoned shortly after their release.
60% of the extensions in the CWS (Chrome Web Store) have never been updated; half of the extensions known to be vulnerable are still in the CWS and still vulnerable 2 years after disclosure
[source]
The Chrome Web Store automatically scans and in many cases manually reviews the initial submission and every update to an extension. While that process flags many malicious or insecure submissions, a lot still slip through.
API compromised
Some extensions require talking to an external API. They might send data to it, receive instructions, or, in the worst case, fetch code snippets to execute. Those APIs come with their own potentially vulnerable infrastructure and can’t be vetted by the Chrome Web Store.
Malicious developer
The developer of an extension might have evil motives to begin with, develop them over time, or hand over maintenance to someone who does.
Extension is sold
This is very common. When an extension gains popularity, the developer becomes overwhelmed by the number of bug reports and feature requests. Companies in the data selling business offer to take over or purchase the project, often under false pretenses. Afterwards, they monetize it, exfiltrate data, and occasionally inject malware.
This happened to AdBlock, Nano Adblocker, The Great Suspender, and uBlock (which led to the creation of uBlock Origin).
Bad code sneaks in
Most developers publish the code to their browser extensions in public repositories. Other people can read the code and suggest concrete changes (so-called pull requests). Attackers sometimes try to hide backdoors in seemingly harmless code contributions in the hopes that the developer doesn’t detect them and accepts the changes.
Developer gets compromised
Having indirect control over millions of users’ web browsing makes the developers of popular extensions attractive targets for hackers. They are confronted with more phishing attempts and social engineering.
User installs fake lookalike
Many malicious extensions claim to be authored by an official source but contain malware instead.
There are many cases of popular extensions being copied. They get hundreds of thousands of installs, have stellar reviews, and otherwise look legit.
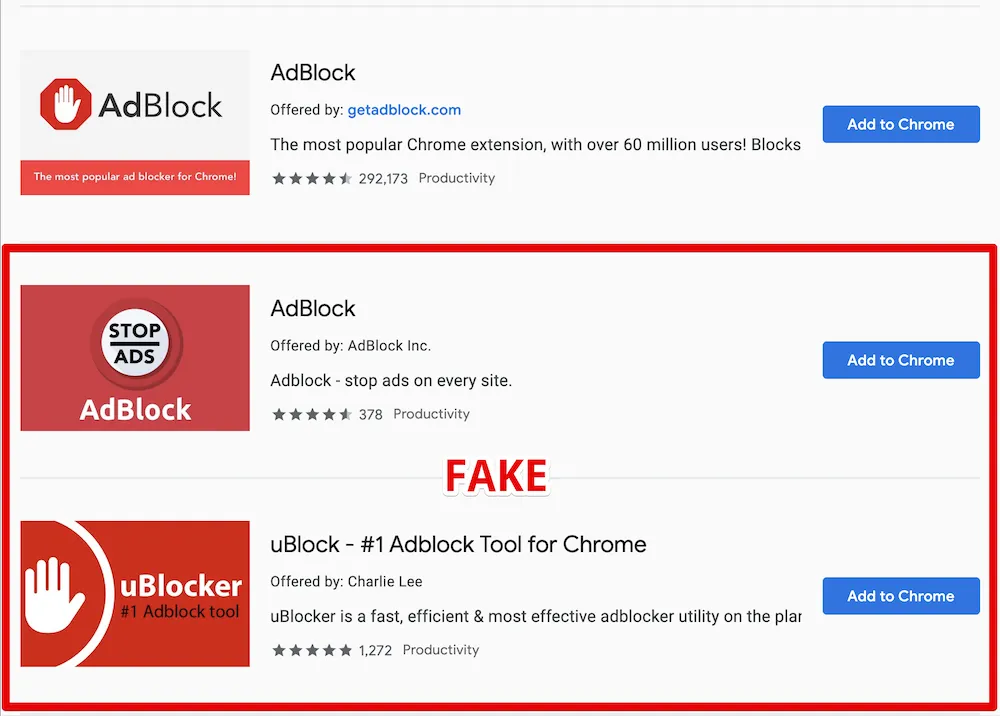
Source: AdGuard
How to Protect Yourself
To begin with, you should know what extensions you have currently installed (3 dots in the upper right corner > Extensions > Manage extensions). Disable or remove the ones you don’t recognize or don’t need anymore.
Limit site access
From here you can click Details on an extension to reach the Site Access setting. By default, many extensions require and request the permission to read and change data on all sites. If you only need an extension sometimes, you can change its site access setting to “On click”. This means the extension will only have access to your active tab once you click its icon in the toolbar (pin its icon for quicker access).
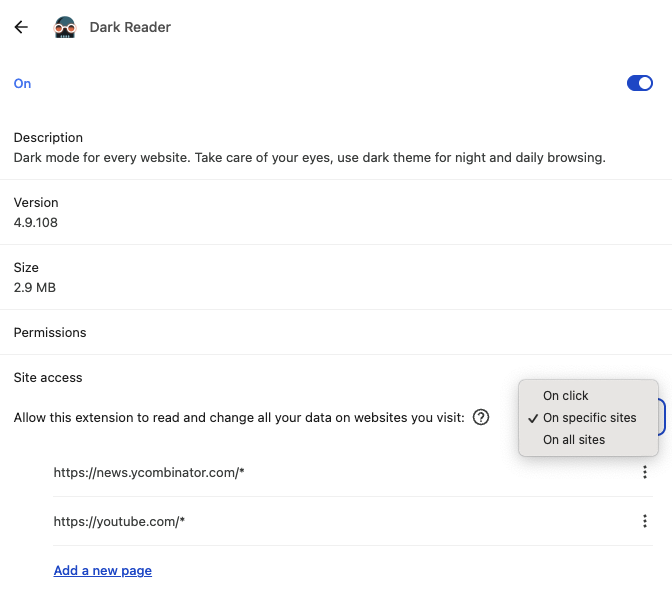
If you want an extension to always have access to a few sites (without having to click the icon), you can select “On specific sites”. You can still click the icon to have it available on sites you don’t list here. Note that this setting only works for some extensions (it depends how they were programmed).
Separate Chrome profiles
Extensions are only installed for the active Chrome profile. If you use your device both for personal and work browsing, I recommend having two profiles. You could even consider creating a third profile where you install and use extensions you don’t trust.
Find alternatives
In some cases extensions were added to supplement a missing feature that has since been added. In other cases, a native solution might be inferior but “good enough”, e.g. Grammarly vs OS-level spell-checking, or DarkReader vs chrome://flags/#enable-force-dark.
For more technical users, some features might be replaceable with OS-level tools like KeyboardMaestro or BetterTouchTool (which come with their own risks, of course).
Vet legitimacy
These are the things I look at to assess the legitimacy and risk of an extension. I’ll do this with the example of uBlock Origin Lite.
- Number of users: A low number can be a bad sign.
- Average rating and number of ratings: Should ideally have 1,000+ ratings and an average of 4.0 or higher.
- Last updated: If it hasn’t been updated in a long time, it might not be maintained anymore and thus won’t receive security patches.
- Find the source code repository (for technical users)
- Some developers link to it in the extension description; here I had to search for it online.
- Note that there is no guarantee that the code in the repository matches what you would install from the Chrome Web Store. The more secure and cumbersome way is to download the CRX file and read the code directly, e.g., with crxviewer.
- Now I look at the last commit, code frequency (a high frequency means it’s actively maintained, which is good), number of contributors (a high number increases the risk that one actor is malicious).
- I also skim the issues, sorting them by total comments and total reactions.
- I briefly research the developer.
- In this case, I only find their GitHub (they have 5.4k followers and have been active since 2011 - both good signs) and X account, as well as a minimal website.
Build from source
For technical users only. If you really need an extension but don’t trust the developer, you can:
- Fork the source code
- Read/audit the code
- Compile the project yourself
- Go to Chrome extensions
- Enable developer mode
- Load unpacked and select the build folder
Note that this will put the onus of updating the extension on you. You will no longer benefit from the Chrome Web Store’s review process nor any security patches found by the developer or the community.
How to Protect Your Organization
If you are in charge of protecting your team against these risks, there are a few things you can do. I’ll assume you’re using Google Workspace, but similar controls exist, e.g., for Microsoft.
A note on updates
Chrome updates extensions automatically every 5h. Unless you’re launching Chrome with a command-line flag, you can’t easily change this. Updating extensions doesn’t require a restart.
Enforce separate Chrome profile
If your organization uses work devices, this doesn’t apply. For everyone else, using separate Chrome profiles for work and personal browsing can reduce the number of extensions a user needs on a given profile.
Enforce this setting in Google Admin to prepare for the next step.
Only allow vetted extensions
Ask your team which extensions they currently use on their work profile. If you enrolled your users’ browsers in Chrome Enterprise Core, you can see a list under Admin Console > Devices > Chrome > Apps & extensions > Extension report.
For each extension you want to allow, configure an installation policy (Admin Console > Devices > Chrome > Apps & extensions > Users and browsers > Add).
Once you’ve handled all cases, give your team a heads up before blocking all extensions not on the allowlist: Devices > Chrome > Apps & extensions > User app settings > Allow/block mode.
The “Users may request extensions” option only works when you enrolled your users’ browsers with Chrome Enterprise Core.
Allow install
If you trust the developer (like Google) or you decide the risk is worth it.
Force install
Useful to install extensions everyone needs, e.g., your organization’s password manager. Use this sparingly. The fewer extensions, the better.
Customize permissions
If you vetted an extension, decided to allow it, but want to protect against permission creep (when a harmless extension requests more permissions later on). Unfortunately, this doesn’t cleanly map to the required permissions defined in an extension’s manifest.json.
You can also change this globally: Devices > Chrome > Apps & extensions > Permissions and URLs.
Overall, this is easy to misconfigure and thus impact users. I recommend other options.
Block hosts
Enrolled browsers only
This setting will only work with enrolled browsers as part of Chrome Enterprise Core. If you’re not a using mobile device management software, you probably can’t use this.
An ad blocker doesn’t need to read the data on your internal tools like Gmail or Slack. You can provide a list of websites the extension will not have access to. You can also make this a global default (which I don’t recommend).
Here’s a sample blocklist for common tools. I recommend you complement this with other tools as well as any banks your organization uses.
https://*.1password.com
https://*.slack.com
https://*.zoom.us
https://www.notion.so
https://*.github.com
https://teams.microsoft.com
https://outlook.office.com
https://*.sharepoint.com
https://*.atlassian.net
https://mail.google.com
https://drive.google.com
https://meet.google.com
https://calendar.google.com
https://contacts.google.com
https://chat.google.com
https://admin.google.com
https://keep.google.com
https://docs.google.com
https://sheets.google.com
https://slides.google.com
https://classroom.google.com
https://forms.google.com
https://tasks.google.com
https://voice.google.com
https://groups.google.com
https://photos.google.com
https://hangouts.google.comSelf-host CRX files
This is a technically complex edge case I list for the sake of completeness. It’s relevant when you want to allow but not force users to install an audited version of an extension.
As described earlier, you can build an extension from source, then host the CRX file along with an update manifest and specifically allow (or force install) this by choosing “Add an isolated web app”.
Recommendations for Common Extensions
If you’re wondering what to do about an extension not listed here, feel free to send me a quick email: [email protected].
Remember: Fewer extensions mean less attack surface. I’m defaulting to blocking most nice-to-have extensions in a work context - loosen as needed.
| Extension | Personal Use | Org Policy | Notes |
|---|---|---|---|
| 1Password | Keep | Force-install if used org-wide; otherwise block | Trusted developer |
| Adobe Acrobat | Keep | Allow | Trusted developer but consider using an OS-level alternative for more control |
| Adblock | Remove | Block | Use uBlock Origin instead (their Acceptable Ads model is questionable) |
| Adblock Plus | Remove | Block | Use uBlock Origin instead (their Acceptable Ads model is questionable) |
| Bitwarden | Keep | Force-install if used org-wide; otherwise block | Trusted developer |
| Calendly | Keep with site access to on click or the sites you need it on | Block | Reputable developer, but consider if necessary |
| Chrome Remote Desktop | Remove unless needed | Block unless needed for your team | Attackers sometimes ask their victims to install this to grant them full remote access. Only keep if you have an active use case. |
| DarkReader | Keep with site access to on click or the sites you need it on | Block | Requires broad permissions. Consider native but inferior alternative: chrome://flags/#enable-force-dark |
| Google Docs Offline | Keep | Allow | Trusted developer |
| Google Translate | Keep | Allow | Trusted developer. Note that Chrome has some translation features built-in. |
| Grammarly | Keep | Block | Requires broad permissions. Consider using OS-level spell checking instead. |
| HTTPS Everywhere | Remove | Block | Deprecated; browsers enforce HTTPS by default now |
| I don’t care about cookies | Remove | Block | Was bought by Avast. Not actively maintained. |
| I still don’t care about cookies | Remove | Block | Not actively maintained. Consider enabling the “EasyList/uBO – Cookie Notices” list in uBlock Origin Lite instead. |
| Keeper Password Manager | Keep | Force-install if used org-wide; otherwise block | |
| LastPass | Remove | Block | LastPass has a long history of security incidents and I strongly advise switching to 1Password or Bitwarden |
| Loom | Enable when needed | Block | Requires very broad permissions. Consider the desktop apps for more control. |
| News Feed Eradicator | Keep | Block | Only needs permissions for the sites you enable it for |
| Okta | Remove | Force-install if used org-wide; otherwise block | Reputable developer. Should only be needed in a work context. |
| Privacy Badger | Keep | Block | Some overlap with uBlock Origin. Only install if you need the additional features. |
| Readwise | Keep with site access to on click | Block | Requires broad permissions |
| Tampermonkey | Keep but limit site access to the sites you need it on | Block | Requires broad permissions |
| uBlock Origin | Remove | Block | Not available for Chrome anymore. Use on supported browsers. |
| uBlock Origin Lite | Keep | Allow with blocklist | See above for a sample blocklist |
| Video Speed Controller | Keep with site access to on click (“on specific sites” won’t work here) | Allow with allowlist | Requires broad permissions |
| Zoom | Remove | Block | Not needed to join meetings. Requires access to Google Calendar. |